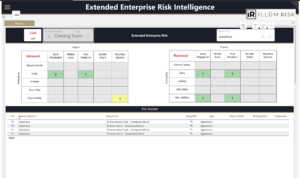
– Extended Enterprise Risk Intelligence
– Extended Enterprise Risk Intelligence
Your Vendor Ecosystem Is Your Largest Unmonitored Attack Surface
Over 60% of data breaches now involve a third party. When the next major vendor breach is announced, EERI tells you whether you're exposed in hours — not weeks.
[eR] Extended Enterprise Risk Intelligence gives your organization a continuously updated, enterprise-wide view of every vendor relationship: who they are, what they can access, and what their security posture looks like right now.
The Problem
You're managing third-party risk with tools built for a different era
Your vendor ecosystem has quietly become one of the most consequential risk surfaces your organization operates. Not because you made bad choices — because the operating model changed. SaaS proliferation, MSP dependencies, and shadow IT have expanded your actual vendor footprint 40–60% beyond what IT tracks today.
Annual questionnaires aren't a risk program
Most mid-market organizations rely on annual questionnaires and contract language as their primary vendor risk controls. That's a compliance artifact, not a risk management program. A vendor's security posture can change dramatically in 90 days. Between assessment cycles, you're operating blind.
When a vendor breach hits, the clock is already running
When a major vendor incident is announced — SolarWinds, MOVEit, Change Healthcare — most organizations spend weeks manually determining whether they're affected. During those weeks, exposure compounds, regulators start calling, and your board wants answers you can't produce. Over 60% of data breaches now involve a third party, and most organizations find out they're affected from news headlines, not their vendor risk program.
Regulators have noticed
FFIEC, NAIC, HIPAA BAA, and SOC 2 vendor oversight requirements are tightening. Examiners are moving beyond "do you have vendor contracts" toward "demonstrate your continuous monitoring program." Mid-market organizations that can't produce formal, evidence-backed vendor oversight documentation are receiving findings — and those findings have consequences.
The real risk sits one layer deeper
Even organizations with a vendor inventory rarely map what sits beneath it. Your vendors have vendors. When a critical technology provider three layers deep is compromised, your direct vendor relationship gives you zero visibility into the exposure. Nth-party supply chain risk is the blind spot that point solutions miss entirely.
What [eR] EERI Delivers
Know every vendor — not just the ones IT tracks
Build and maintain a complete, tiered vendor inventory classified by criticality, data access, and operational dependency. EERI typically discovers 40–60% more vendor relationships than organizations believe they have — including vendors with production system access that no one knew about.
Monitor continuously — not annually
Real-time monitoring of vendor security posture across threat intelligence, breach signals, and configuration risk. Your oversight is calibrated to actual risk: high-criticality vendors with sensitive data access receive proportionally more scrutiny than low-risk commodity suppliers.
See the supply chain beneath your vendors
Map nth-party dependencies — your vendors' key technology providers — for supply chain exposure visibility beyond the first tier. When a breach hits a platform three layers deep, you already know whether it touches your environment.
Quantify breach exposure in hours
When a vendor incident is announced, EERI immediately maps your direct and indirect dependencies to quantify exposure. No manual investigation. No scrambling. You tell your board and your regulator exactly where you stand — the same day.
Produce regulatory-ready evidence on demand
Pre-built compliance documentation for FFIEC, NAIC, HIPAA BAA, and SOC 2 vendor oversight requirements. When the examiner asks for evidence of a mature third-party risk program, the package is already built.
Make third-party risk part of your complete risk picture
EERI findings feed directly into the unified iLLÜM Risk Insight risk register. Third-party risk isn't a separate spreadsheet or a standalone program — it's integrated into your organization's complete risk view.
How It Works
EERI deploys in this week. iLLÜM handles the heavy lifting — your team validates, not project-manages.
Weeks 1–2: Discovery & Population
iLLÜM maps your complete vendor ecosystem — including SaaS, MSPs, and shadow IT dependencies your team may not track today. Vendors are populated into EERI with initial data classification.
Weeks 3–4: Classification & Monitoring Activation
Vendors are tiered by criticality, data access, and operational dependency. Continuous monitoring activates across threat intelligence, breach signal, and configuration risk feeds. Nth-party supply chain mapping begins.
Weeks 5–6: Regulatory Mapping & Go-Live
Compliance documentation is generated against your applicable regulatory frameworks. EERI integrates into Risk Insight. Your team reviews, validates, and your continuous third-party risk program goes live.
After deployment, EERI runs continuously. New vendors are classified as they're onboarded. Monitoring signals update in real time. When a vendor incident occurs, exposure identification is automatic.
Who It's For
[eR] EERI is built for mid-market organizations with 200–2,500 employees, 20+ active vendor relationships, and $50M–$2B in revenue — organizations where third-party risk is real but dedicated TPRM teams aren't.
Industries: Financial services (credit unions, community banks, insurance), healthcare, manufacturing, and professional services.
Buyers: CISOs, CROs, VPs of Information Technology, VPs of Procurement, and Vendor Management Directors who know their current vendor risk approach won't survive the next regulatory examination or vendor breach.
What You Get
A complete, operational third-party risk management program — not a point solution.
-
Continuous vendor monitoring — Real-time security posture intelligence across your entire vendor ecosystem, not annual snapshots
-
Breach exposure identification — Know whether you're affected within hours of a vendor incident announcement
-
Nth-party supply chain visibility — See the dependencies beneath your vendors that create hidden exposure paths
-
Tiered vendor classification — Oversight effort calibrated to actual risk — criticality, data access, and operational dependency
-
Regulatory evidence packaging — Pre-built compliance documentation for FFIEC, NAIC, HIPAA BAA, and SOC 2 vendor oversight requirements
-
Integrated risk picture — Third-party risk findings feed directly into iLLÜM Risk Insight — one unified view of organizational risk
Customer Results
First positive TPRM finding in examination history
A mid-sized regional credit union had a formal vendor risk program with an established partner. EERI onboarded 300 vendors, applied tiered classification by criticality and data access, and established continuous monitoring. During the subsequent examination, the auditor specifically cited their vendor risk program as a strength!
Compliance documentation in 6 weeks vs. 3 months
A mortgage banker needed to demonstrate compliance with NAIC Model Law vendor oversight requirements for state regulatory examination. EERI mapped their entire vendor ecosystem, applied regulatory tiering, and generated a complete evidence package. The carrier achieved full compliance documentation in 6 weeks — compared to an estimated 3-month manual effort.
"When the MOVEit breach was announced, we knew within 24 hours whether we were affected. Before EERI, that would have taken us two weeks of manual investigation."
"Our NCUA examiner specifically called out our vendor risk program as a strength for the first time. That has never happened before."
"We thought we had 35 vendors. EERI found 258 — including two with production database access that IT didn't know about."
The Next Major Vendor Breach Will Happen. Will You Be Ready?
Ask yourself:
-
When the next vendor breach is announced, how quickly can you tell your board and your regulator whether your organization is affected?
-
How many of your vendors have access to production systems or sensitive customer data? Is your vendor count even accurate?
-
If your regulator examined your third-party risk program tomorrow, could you demonstrate continuous monitoring — or just an annual questionnaire and a contract?
Your competitors are already building continuous vendor risk programs. Regulators are already asking for them. The question isn't whether you need one — it's whether you build it before or after the next examination finding.
Talk to iLLÜM about what a continuous third-party risk program looks like for your organization. No pitch deck — just an honest assessment of where your vendor risk program stands today and what it takes to get where regulators expect it to be.